BitLocker Decryption Key Retrieval via TPM Bus Sniffing
Project: BitLocker Bypass with TPM Hardware Hacking
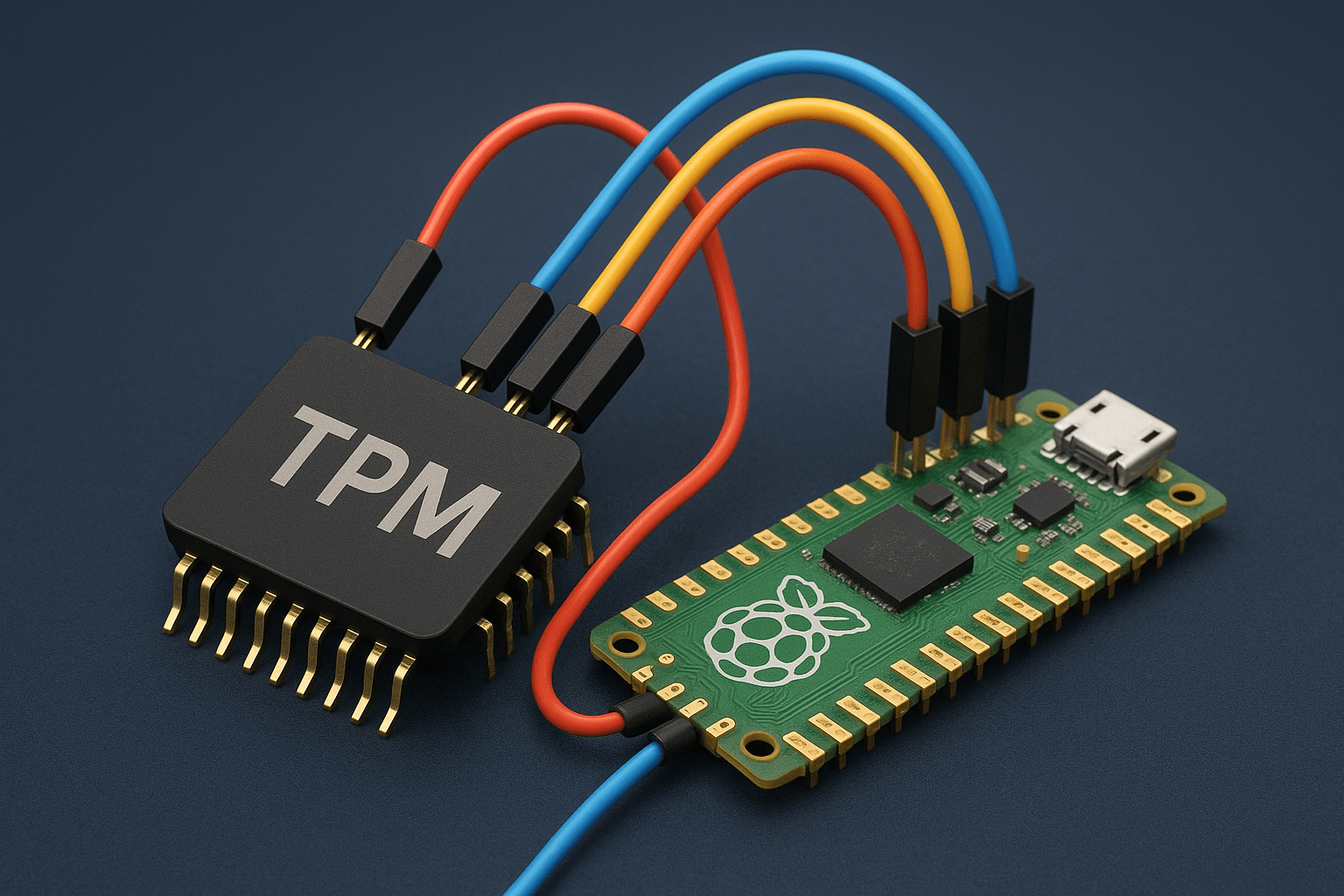
Description: Performed a hardware-based attack against BitLocker by targeting the Trusted Platform Module (TPM). Leveraged side-channel access to intercept the unencrypted exchange of BitLocker keys between the TPM and CPU during system boot. The attack was conducted without removing the hard drive, instead focusing on sniffing communication lines using a Raspberry Pi Pico with jumper wires. Delivered findings with detailed mitigation strategies against physical attacks on TPM-bound devices.
Key Features:
- Hardware sniffing of TPM communication during boot process
- Extraction of BitLocker decryption keys without removing the drive
- Use of Raspberry Pi Pico for low-cost hardware interfacing
- Demonstrated vulnerability in systems relying solely on TPM security
- Provided countermeasures such as PIN-enabled TPM protection and hardware tamper detection
Technologies & Tools Used:
- Raspberry Pi Pico
- Jumper wires & hardware interfaces
- Logic analyzers (for bus sniffing)
- Python (for data parsing and automation)
Use Case: This project demonstrated the risks of relying solely on TPM for BitLocker security in enterprise and personal laptops. By simulating real-world hardware attacks, clients were made aware of the importance of multi-factor BitLocker protections (PIN or USB keys) and physical device hardening.